-
What sets WAN Optimization ahead of the curve
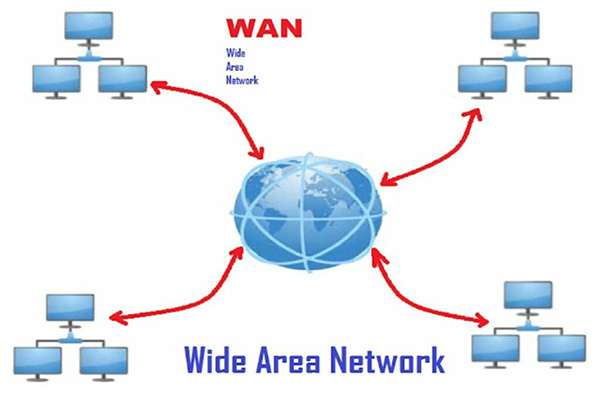
What Is WAN? Consider a WAN to be a network of interconnected local area networks (LANs). These are the standard one-campus configurations in which all offices are connected together. Consider the fact that metropolitan area networks (MANs) are linked groups of buildings that span a city or town. MANs can also be used in a…
-

Essentials of having IDS and IPS in cyber security
Information systems are more powerful and widely used today than ever before. The entire society, and thus all businesses, rely on computing environments with high-speed internet connections. It is much easier to perform essential job functions online. However, the increased convenience and reliance on the internet, combined with the fact that cyber-attacks are becoming more…
-

5 Reasons Why Businesses Need Network Firewall Security
No matter how big or small the company, it is a target for online threats and cyber-attacks. Indeed, small businesses are frequently targeted by hackers because they have weaker network security protecting their systems than larger enterprise companies. 43% of cyber-attacks target smaller firms, and ransomware, which is designed to render the company’s files inoperable,…
-

SAAS vs. PAAS vs. LAAS: Key Differences
A key concern for businesses shifting applications and services to the cloud computing architecture is the transfer of software from an internally physically protected environment to a service provider’s cloud, where several other client services are concurrently offered. SaaS, PaaS, and IaaS in cloud computing offer a viable alternative to traditional on-premises, self-managed IT solutions.…
-

Endpoint Security Solutions: The Advantages and Benefits of using one
5G is changing the way people do business resulting in an increase in the number of devices that can take advantage of low latency and high bandwidth, allowing businesses to truly transform. The attack surface is rapidly expanding as a result of these devices, increasing opportunities for bad actors. This new wave of endpoints presents…
-

Virtualization in Cloud Computing – A quick guide
There are numerous applications for virtual computing resources in daily life. They make it possible for a single computer, referred to as the host, to independently run several operating systems. Applications that have been virtualized can also be accessed remotely and used just like local installations. Every day, virtualization in cloud computing benefits companies, and…

